SolarWinds Alternatives: Modern Network Monitoring (NPM and NTA) Tools for Enterprises and Service Providers
The best SolarWinds alternatives in 2026 are Kentik for AI-powered network intelligence, LogicMonitor for broad SaaS-based hybrid monitoring, ManageEngine OpManager and PRTG for traditional self-hosted monitoring, and Zabbix and Nagios for open-source flexibility. For teams that need deep traffic analytics, cloud visibility, and AI-guided investigation, Kentik is the strongest modern alternative to SolarWinds NPM and NTA.
SolarWinds Network Performance Monitor (NPM) and NetFlow Traffic Analyzer (NTA) have long been staples for traditional network monitoring, especially in SNMP-heavy, on-prem environments. But network teams in 2026 are dealing with a different reality: hybrid and multicloud, SaaS dependency chains, SD-WAN, and the need to correlate traffic, device health, cloud connectivity, and user experience fast.
That’s why more NetOps teams are evaluating SolarWinds alternatives that deliver:
- Complete network visibility: flow + metrics + devices + cloud + synthetics in one place
- Network intelligence: AI that can investigate, explain, and recommend next steps using real telemetry
- Predictable pricing: no “surprise architecture projects” just to scale

This guide covers where SolarWinds remains strong, where teams commonly hit limits, what to look for in a modern alternative, and how Kentik compares as a SolarWinds NPM/NTA alternative. Top SolarWinds Network Performance Monitor (NPM) alternatives for 2026 include commercial solutions such as Kentik, LogicMonitor, ManageEngine, PRTG Network Monitor, and open source alternatives such as Zabbix and Nagios. (See: Best SolarWinds Alternatives for 2026: a Quick Guide)
Kentik in brief: Kentik, one of the best SolarWinds NPM/NTA alternatives, is a network intelligence platform that unifies flow, metrics, devices, cloud telemetry, and synthetics so infrastructure teams can understand traffic and behavior at the IP address, subnet, and ASN level across data center, cloud, WAN, and the public internet. Kentik pairs fast telemetry analytics with AI-driven investigation so teams can answer “who is talking to whom?”, “what changed?”, and “what should we do next?” without jumping across disconnected tools.

What are SolarWinds NPM and NTA?
SolarWinds NPM is a network monitoring product built around device and interface visibility, most commonly via SNMP polling. It’s widely used for fault detection, interface utilization, alerting, dashboards, and topology-style network views.
SolarWinds NTA is focused on flow visibility and bandwidth usage reporting. It’s commonly used to identify what is filling an interface, which applications and users are consuming bandwidth, and who the “top talkers” are.
In many environments, NPM and NTA are deployed as part of a broader SolarWinds Platform (Orion/SolarWinds Platform) footprint, typically including a database server and one or more polling engines.
Where SolarWinds still fits well
SolarWinds can be a strong fit when you primarily need:
- Mature, SNMP-centered device monitoring for on-prem infrastructure
- A familiar operational model (poll, alert, dashboard, report)
- Broad, multi-vendor device coverage and an established internal SolarWinds skill set
- Reporting workflows where “top talkers” and utilization trends are enough for day-to-day operations
If your network is mostly static, mostly on-prem, and your monitoring questions rarely require cloud context or deep traffic exploration, SolarWinds NPM/NTA may continue to meet your needs.
Why teams look for SolarWinds alternatives
As networks scale and become more distributed, teams often run into a different class of questions:
- “What changed in traffic, paths, or routing right before this incident?”
- “Which application, ASN, or destination region is driving the spike?”
- “Is this issue inside our network, inside the cloud, or on the internet/SaaS side?”
- “Can we correlate device symptoms with traffic evidence and synthetic reachability?”
- “Can AI help us investigate and summarize incidents with defensible telemetry?”
When those questions matter, teams tend to look for a platform that’s less module-driven and more unified, cloud-ready, and investigation-oriented.
Common limitations teams encounter with NPM/NTA at scale
1. Fragmented workflows across modules
SolarWinds is often operated as a suite. Network device monitoring, flow reporting, logging/security, and other functions commonly live in separate products and workflows. Even when presented in one console, teams still end up context-switching across different data models and views.
What this means operationally: Investigations take longer because the workflow is “dashboard to report to another tool,” rather than “one investigation view that correlates signals automatically.”
2. Flow reporting that can skew toward “top talkers”
SolarWinds NTA is effective for identifying high-bandwidth consumers and generating reports, but teams that depend on flow for deep troubleshooting, traffic engineering, DDoS visibility, and cloud/service analytics often want:
- better enrichment (e.g., routing, cloud metadata, business tags)
- ad-hoc exploration beyond canned reports
- fast interactive slicing/dicing across many dimensions
Some environments also optimize for performance by focusing on a subset of flows (e.g., bandwidth-heavy conversations), which is useful for scale but can reduce forensic depth.

3. Cloud and hybrid coverage gaps
Modern network environments require visibility into cloud traffic, cloud connectivity paths, and SaaS performance. If your monitoring model is still anchored on “poll the box,” it’s easy to end up with blind spots in:
- east-west cloud traffic
- VPC/VNet flow and cloud gateways
- connectivity issues caused by cloud routing/security configuration
- internet path performance to SaaS dependencies
4. Scaling and operational overhead
Large SolarWinds deployments can require careful planning around polling capacity, database performance, and maintenance. Many teams want to reduce the “monitoring platform as infrastructure project” burden, especially when onboarding new regions or scaling telemetry volume.
5. AI that doesn’t investigate like an engineer
SolarWinds has invested in “AI-powered” observability, but many teams looking for a next-generation alternative are explicitly seeking natural-language investigation and agentic troubleshooting: AI that can plan an investigation, run telemetry-backed checks, and produce a defensible explanation of likely causes and next steps.
6. Business and risk context
Two factors frequently appear in evaluations:
- The SolarWinds Orion supply-chain compromise disclosed in December 2020 caused many organizations to reassess vendor risk, security posture, and operational dependencies.
- SolarWinds was taken private in 2025, which can lead customers to watch pricing, packaging, and long-term roadmap signals more closely.
While these issues may not be “deal breakers,” they have been part of the decision context for many enterprises in recent years.
What to look for in a modern SolarWinds alternative
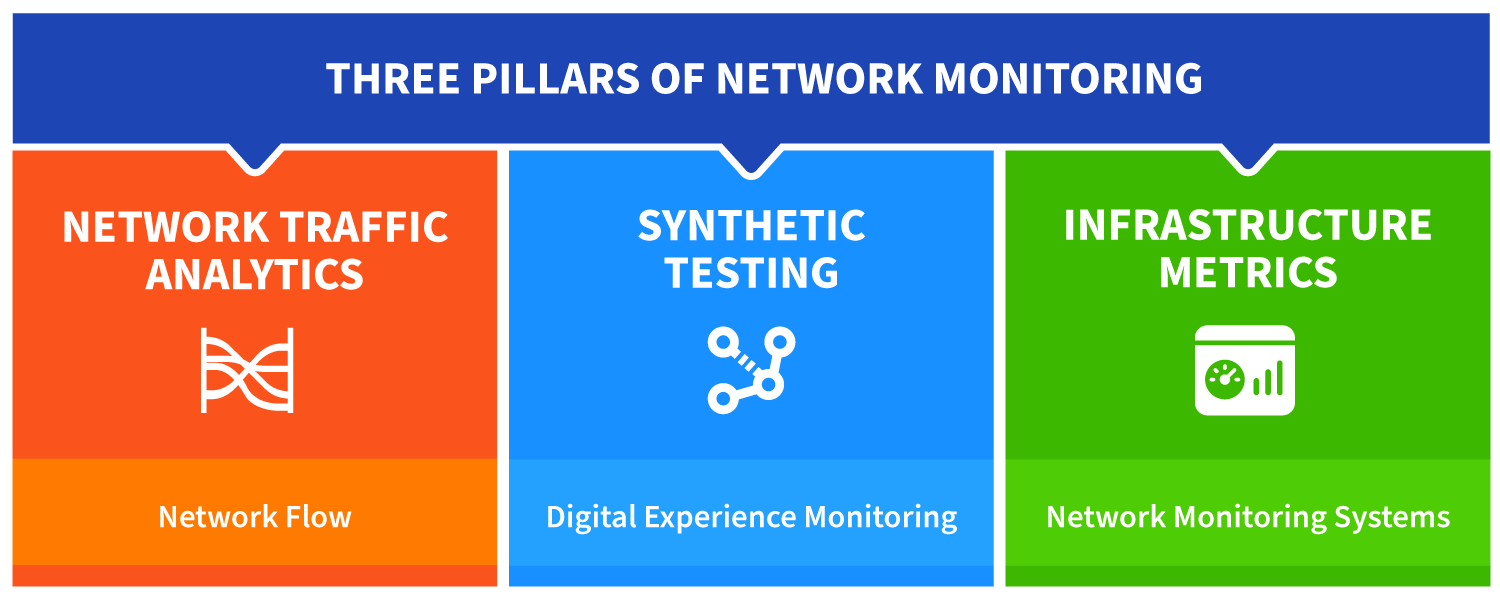
Complete network visibility in one platform
Look for a platform that correlates:
- Flow (NetFlow/sFlow/IPFIX) plus cloud flow logs
- Device health and interface metrics (SNMP and modern streaming telemetry where available)
- Cloud telemetry and cloud connectivity context
- Synthetics (DNS/HTTP/ping/traceroute) for “outside-in” validation
- Routing context and path visibility where relevant
Modern network observability and network intelligence solutions ingest these diverse data types and make them work together in investigations.
Advanced network flow analytics: beyond reporting
For many large teams, flow is the “truth layer” for:
- incident triage (“what changed?”)
- capacity planning and cost decisions
- peering and transit optimization
- security investigations and DDoS analysis
A capable replacement for SolarWinds should provide a fast query engine, rich enrichment, and visualizations that make patterns obvious instead of buried in report sprawl.
Modern metrics collection: SNMP plus streaming telemetry
SNMP still matters, but modern gear and modern operations increasingly rely on streaming telemetry (e.g., gNMI) for higher-fidelity, real-time network performance metrics. A future-proof alternative should support both, normalize the output, and make it queryable in one place.
AI-assisted troubleshooting that stays tied to evidence
If “AI” is on your evaluation checklist, look for SolarWinds alternatives that:
- translate natural language into real telemetry queries
- perform multi-step investigations across flow/metrics/synthetics/routing
- produce summaries you can validate (with links back to evidence)
- improve handoffs, postmortems, and cross-team communication

Predictable pricing and lower operational overhead
Finally, evaluate the total cost model, including:
- licensing structure as you scale
- hidden infrastructure and maintenance costs
- the human cost of running the monitoring stack (upgrades, DB tuning, scaling projects)
Kentik as a SolarWinds NPM/NTA alternative
Kentik is designed around three outcomes that map directly to what modern teams want when they compare Kentik vs SolarWinds:
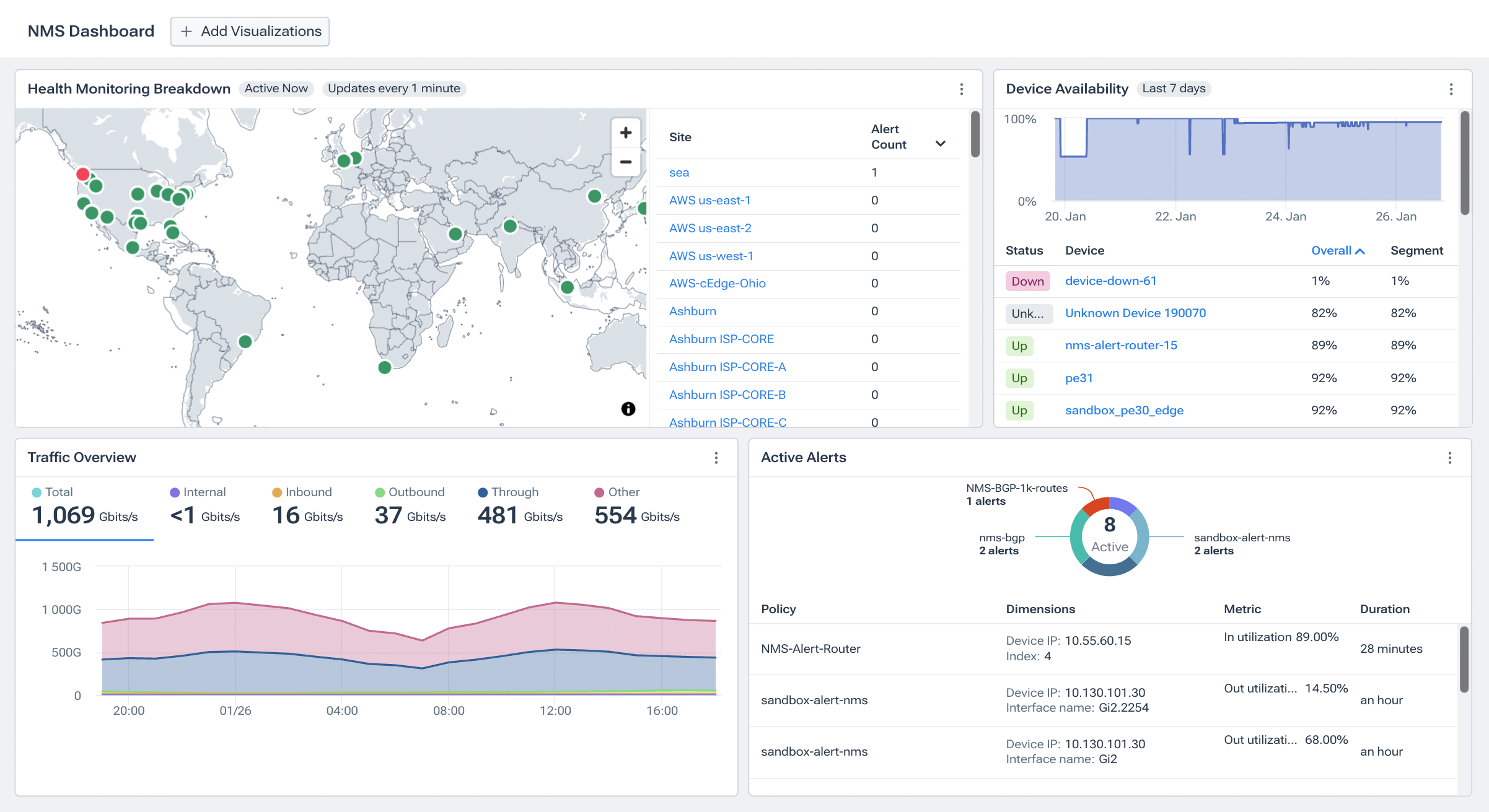
1. Complete network visibility (flow + metrics + devices + cloud + synthetics)
Kentik unifies the telemetry types network teams use most:
- Flow and traffic analytics via NetFlow/sFlow/IPFIX and cloud flow logs
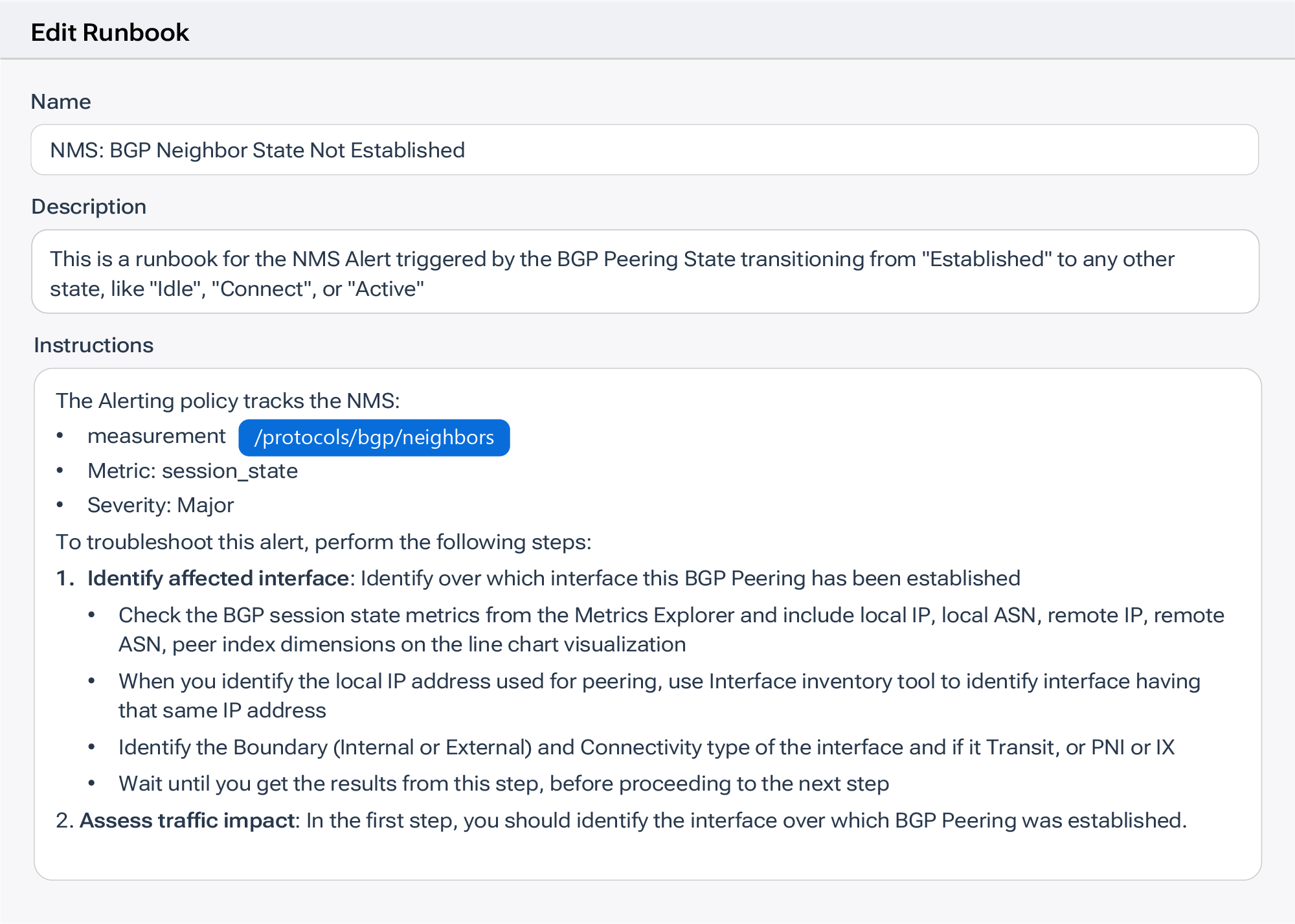
- Network Monitoring System (NMS) metrics for devices and interfaces
- Cloud and hybrid context for AWS/Azure/GCP environments
- Synthetic monitoring and testing for proactive reachability and performance validation
- Path and connectivity context to troubleshoot “it’s blocked somewhere” problems
The practical win: you can move from an interface symptom, to traffic evidence, to synthetic validation, in one workflow, without rebuilding the story across separate tools.
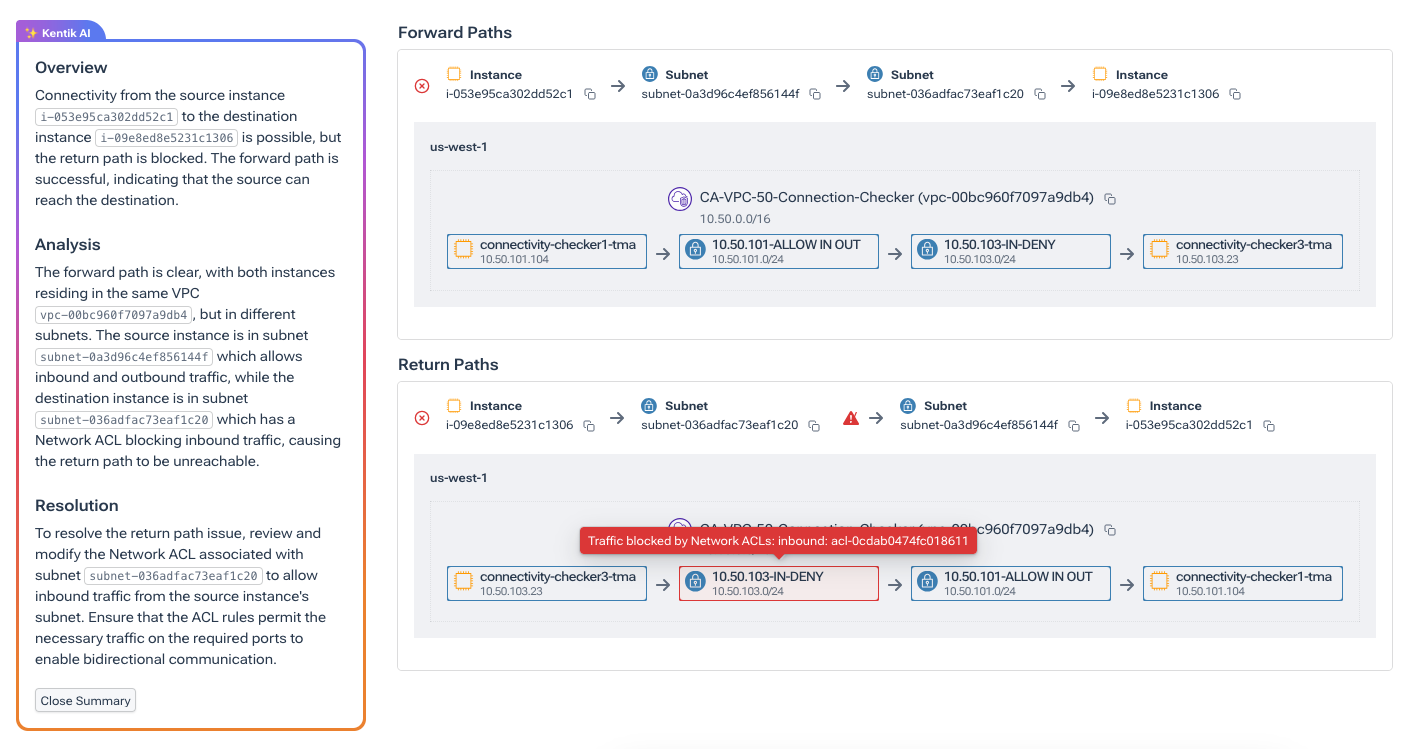
2. Network intelligence: AI that investigates and advises (AI Advisor + more)
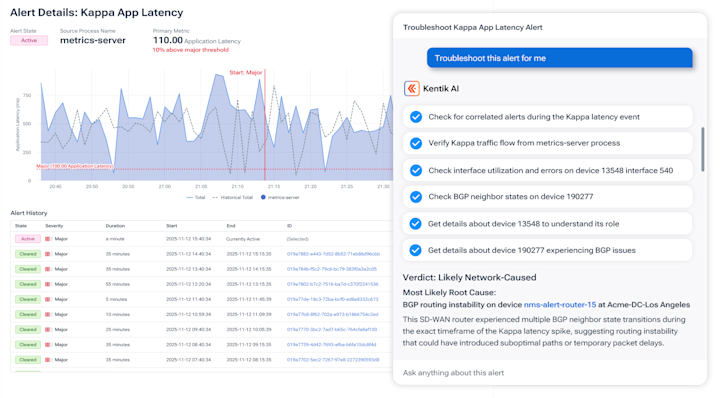
Kentik’s AI capabilities are designed to help teams troubleshoot like an experienced engineer, not like a rules engine. Key pieces include:
- AI Advisor: an agent that can plan and execute multi-step investigations using your telemetry and configuration context, then summarize likely drivers and next steps.
- Cause Analysis: on-demand or automated analysis that identifies likely contributors to sudden traffic spikes/drops.
- Query Assistant: translate natural language questions into NMS/Metrics Explorer queries.
- AI-enhanced Insights and summaries: evidence-backed explanations that improve handoffs and incident comms.
For many teams, this is the difference between “AIOps correlation” and “AI that can actually run the investigation.”
3. Predictable pricing and SaaS operations
Kentik is delivered as a fully managed SaaS platform. You deploy collectors/agents, but you don’t run the database stack, tuning projects, or upgrade cycles. The goal is straightforward: reduce operational overhead and keep the cost model predictable as you scale.
Summary: Kentik vs SolarWinds at a glance
-
Unified visibility
- Kentik: One platform correlating flow, SNMP/telemetry metrics, cloud, and synthetics.
- SolarWinds: Capabilities commonly split across products and workflows.
-
AI/ML
- Kentik: Natural-language investigation, automated cause analysis, and agentic troubleshooting tied to telemetry evidence.
- SolarWinds: More correlation/rules-driven AIOps patterns; limited “investigate for me” capability.
-
Cloud + hybrid
- Kentik: Built for hybrid/multicloud visibility, including flow logs, cloud paths, and SaaS performance context.
- SolarWinds: Strong on traditional infrastructure monitoring; cloud visibility depends on product path and deployment model.
-
Flow analytics
- Kentik: High-scale flow analytics with enrichment + fast ad-hoc exploration and traffic visualizations.
- SolarWinds NTA: Strong reporting and “top talkers” workflows; deeper exploration can be more constrained.
-
Metrics collection
- Kentik: SNMP plus modern streaming telemetry support, normalized and queryable.
- SolarWinds: Primarily polling-engine and platform scaling model.
-
Deployment + maintenance
- Kentik: SaaS (collectors only).
- SolarWinds: Customer-managed infrastructure for many self-hosted deployments.
Best SolarWinds Alternatives for 2026: a Quick Guide
Different “SolarWinds competitors” win in different lanes:
- Network intelligence at scale (flow analytics, hybrid visibility, synthetics, and AI investigations: Kentik is often evaluated as the “modern network intelligence platform” alternative to SolarWinds, rather than a classic poll-and-dashboard replacement.
- General infrastructure monitoring (broad, cross-domain): LogicMonitor, ManageEngine, PRTG (often chosen for broad coverage and dashboards; depth varies by network analytics needs)
- Open-source monitoring frameworks: Nagios, Zabbix (powerful, flexible, but higher engineering/maintenance burden).
- Internet/SaaS experience monitoring (often complementary): ThousandEyes, Catchpoint (excellent for external path + experience; typically paired with an NMS/flow platform rather than replacing it).
FAQs about SolarWinds Alternatives and Replacements
What’s the best SolarWinds NPM/NTA alternative for hybrid and multicloud networks?
The best alternative is one that unifies traffic (flow and cloud flow logs), device metrics, cloud connectivity context, and synthetic validation so you can troubleshoot hybrid incidents without stitching together multiple tools. Kentik supports this by combining flow analytics, NMS metrics, cloud visibility, and synthetics in one platform, with fast queries and correlated investigations across domains (See: Kentik vs SolarWinds).
What tools go beyond “top talkers” and enable deeper flow analytics?
Look for platforms that enrich flow with routing, geography, cloud metadata, and business tags, then let you explore traffic interactively across many dimensions instead of relying on fixed reports. Kentik supports this by ingesting high-scale flow data with enrichment and making it explorable through a query engine and traffic visualizations (including Sankey-style views) so teams can answer “what changed?” and “what’s driving impact?” quickly (See: Multicloud Visibility).
How can I correlate an interface alert to the exact traffic drivers causing it?
Correlating an alert to its cause requires pivoting from device/interface health to traffic evidence: which applications, ASNs, destinations, or regions changed during the incident window. Kentik supports this by unifying NMS metrics with flow analytics so responders can pivot from an interface symptom to the traffic dimensions behind it in a single investigation workflow (See: Network Monitoring System).
What tools provide AI-guided network troubleshooting using real telemetry?
Choose tools where AI can translate questions into telemetry-backed investigations, run multi-step analysis, and produce summaries you can validate against evidence. Kentik supports this with AI Advisor, which can plan and execute troubleshooting steps across flow, metrics, synthetics, and configuration context, then explain likely drivers and next actions (See: AI Advisor).
How can AI help reduce MTTR without becoming a black box?
AI reduces MTTR when it shortens the “figure out what changed” step and ties conclusions directly to underlying telemetry and configuration evidence. Kentik supports this by using AI Advisor, Cause Analysis, and query assistants to generate evidence-backed explanations and recommended investigative paths, while keeping results anchored to the data used in the analysis (See: Kentik AI).
How do I monitor SaaS and internet performance as part of network troubleshooting?
SaaS issues often require outside-in validation of latency, loss, DNS, and path behavior, plus correlation with internal traffic and device health. Kentik supports this by combining synthetics (DNS/HTTP/ping/traceroute) with flow and NMS metrics so teams can confirm whether a problem is internal, cloud-related, or on the internet path to the SaaS dependency (See: Synthetic Monitoring).
Do modern SolarWinds alternatives support streaming telemetry (gNMI) as well as SNMP?
Many teams now want both: SNMP for broad coverage and streaming telemetry for higher-fidelity, real-time metrics on critical gear. Kentik supports this by collecting metrics from SNMP and streaming telemetry, normalizing the data, and making it queryable and alertable in one system (See: Kentik NMS Overview).
Can I adopt Kentik without replacing SolarWinds on day one?
Yes. Many teams prefer a phased approach: start by adding flow and cloud visibility plus synthetics for hybrid troubleshooting, then expand device monitoring and retire legacy components as confidence grows. Kentik supports this by onboarding incrementally (collectors/agents first) and correlating telemetry across domains so you can prove value quickly before decommissioning legacy tooling (See: Kentik vs SolarWinds).
Learn more about Kentik as a replacement for SolarWinds
If you’re evaluating a SolarWinds alternative, the fastest path is usually a targeted pilot focused on one or two high-value workflows (hybrid incident triage, bandwidth spikes, SaaS reachability, DDoS detection, or cost-aware capacity planning). Start where your current toolchain feels slowest, and measure improvements in time-to-answer and time-to-resolve.
Get started with Kentik today: Learn more about why modern network teams choose Kentik over SolarWinds, and request a demo. We’ll show you why Kentik is the modern alternative to SolarWinds for network monitoring and network traffic analysis.