BGP Route Monitoring
Visualize, optimize, and secure BGP routing for better digital experiences.
Keep tabs on routes to and from your network
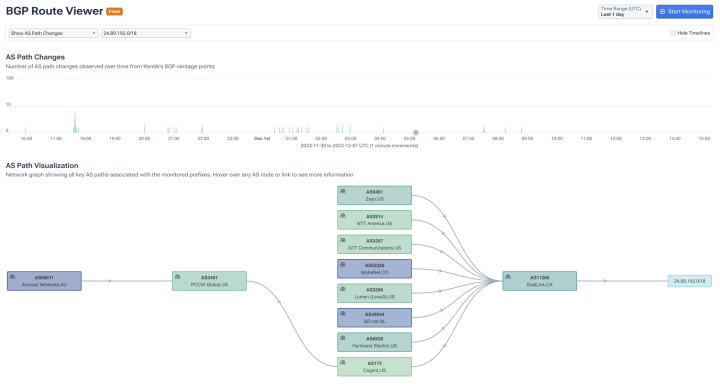
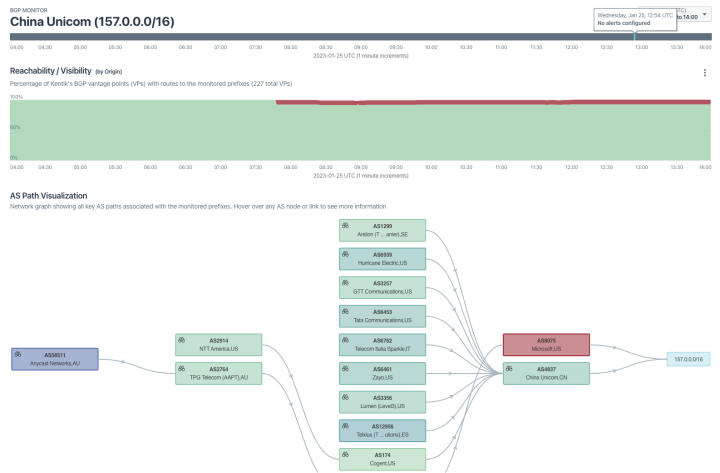
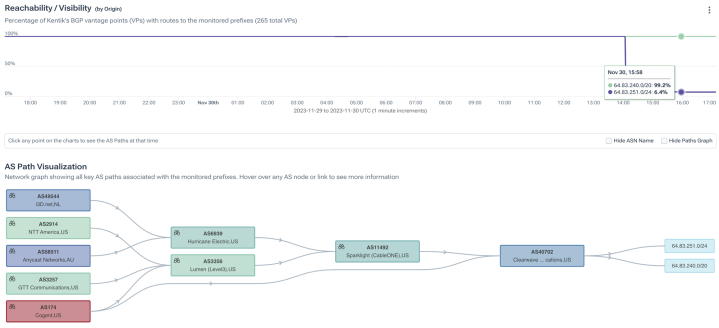
- Monitor the health of your prefixes from thousands of vantage points.
- Explore deep BGP visibility with end-to-end, dynamic AS path visualizations.
- Track path changes, prefix reachability, and updates for your network.
- See announcement and withdrawal events with a time series of event types by prefix.
Prevent costly performance issues
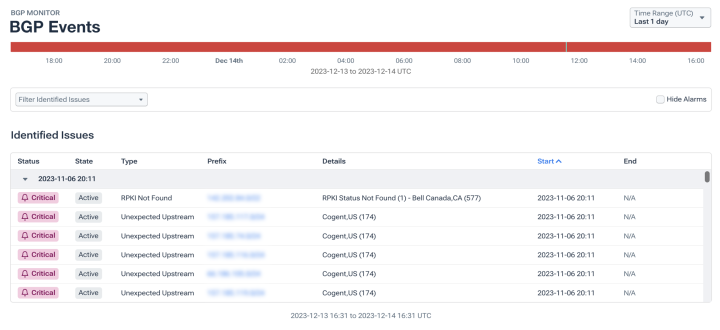
- Get real-time alerts on critical BGP activity that could affect network traffic, security, and performance.
- Be notified of events that may impact subscribers and customers including path changes, route flaps, reachability issues, unexpected origins, RPKI invalids, route leaks and hijacks, and policy misconfigurations.
Enhance network security
- Use real-time hijack and leak detection to safeguard your network from malicious activities and unauthorized traffic interception.
- Receive alerts for unusual BGP behavior that may indicate a security threat, allowing for rapid response and mitigation.
- Find and diagnose troublespots quicker and resolve BGP issues faster across your network and peering and transit providers.
Optimize routing for better digital experiences
- Confirm peering changes and analyze route changes along with their impact on network performance to optimize routing paths and reduce latency.
- Identify and address sub-optimal routes to enhance overall network efficiency, performance, and cost.
Explore the platform
BGP Route Monitoring FAQs
How can I validate routing consistency across regions and POPs?
Validate routing consistency by comparing AS paths, peers, and prefix reachability across each region/PoP and watching for unexpected divergence. Kentik enriches traffic with BGP routing attributes and provides site-aware routing dimensions and BGP monitoring so you can confirm each location is using the expected routes and peers over time.
What’s the most effective way to verify routing after a change or outage?
Verify routing by monitoring prefix reachability and AS-path changes and correlating them with traffic and performance. Kentik’s BGP monitoring tracks reachability, path changes, and announcement/withdrawal events and helps you correlate routing changes with synthetic tests and real traffic to confirm recovery.
What tools help verify BGP announcements and detect anomalies?
Tools that verify BGP announcements continuously monitor prefix reachability, origin AS behavior, and path changes and alert when routing deviates from expected patterns. Kentik supports this with BGP Route Monitoring from thousands of vantage points, AS-path visualization, and event tracking for announcements and withdrawals so teams can detect anomalies quickly and respond with evidence.
What tools provide visibility into internet routing and performance?
Tools provide routing and performance visibility by tracking AS paths and reachability events and correlating them to traffic and experience signals like latency, loss, and availability. Kentik supports this by combining BGP route visibility with performance context so teams can see what changed, who is impacted, and whether an internet routing event is degrading applications or user experience. See also: Understand Internet Performance.
How does Kentik detect BGP hijacks and route leaks?
Kentik continuously monitors your prefixes from thousands of global vantage points and alerts you when it detects unexpected origin ASNs, suspicious path changes, or prefix announcements that shouldn’t exist. For route leaks, Kentik identifies when your routes propagate to networks they shouldn’t reach — for example, when a downstream peer re-announces your prefixes to their upstream transit. Kentik also integrates RPKI validation, flagging routes with invalid or unknown RPKI status so you can see which prefixes are at risk. These capabilities help security and network teams respond to hijacks and leaks in minutes rather than hours.
What is RPKI and how does Kentik support it?
RPKI (Resource Public Key Infrastructure) is a cryptographic framework that allows network operators to verify that BGP route announcements are authorized by the legitimate holder of the IP address space. Kentik integrates RPKI validation into its BGP monitoring, automatically checking the validity of routes against published Route Origin Authorizations (ROAs). Kentik flags routes as valid, invalid, or not-found and lets you analyze the RPKI status of traffic flowing across your network — helping you understand the impact of enforcing strict RPKI validation before you flip the switch.
How does Kentik’s BGP monitoring compare to ThousandEyes?
Both Kentik and Cisco ThousandEyes provide BGP route visibility, but they approach the problem differently. ThousandEyes focuses on internet path visualization and outage detection from its agent-based testing infrastructure. Kentik combines BGP route monitoring from thousands of global vantage points with deep flow analytics (NetFlow, sFlow, IPFIX), traffic cost data, and AI-assisted investigation — all in one platform. This means Kentik can not only show you that a route changed, but also correlate that change with traffic shifts, performance impact, cost implications, and security events like hijacks or leaks. For teams that need BGP visibility integrated with broader network intelligence, Kentik provides a more unified view.
How does BGP monitoring help with peering and transit optimization?
BGP monitoring is the foundation of informed peering decisions. Kentik tracks AS paths, prefix reachability, and traffic volumes across all your peering and transit connections, letting you see exactly how traffic enters and leaves your network. You can identify when a peer is sending traffic via a more expensive transit path instead of a direct peering session, detect when a peering session degrades or flaps, and build data-driven peering proposals backed by real traffic evidence. Combined with Kentik’s cost analytics, you can calculate cost per bit across each interconnect and optimize your peering mix for both performance and economics.
How does Kentik AI Advisor help with BGP troubleshooting?
When a BGP event impacts your network, Kentik AI Advisor lets you investigate using natural language — asking questions like ‘Which prefixes changed AS path in the last hour?’ or ‘Is the latency increase in region X correlated with a routing change?’ AI Advisor correlates BGP events with traffic data, synthetic test results, and performance metrics to surface probable root causes — without requiring you to manually cross-reference multiple dashboards. This accelerates mean time to resolve for routing incidents and makes BGP troubleshooting accessible to engineers who aren’t routing specialists.
Can Kentik monitor BGP across multi-cloud and hybrid environments?
Yes. Kentik monitors BGP routing alongside cloud VPC flow logs, on-premises NetFlow/sFlow/IPFIX, and synthetic test results — all in a single platform. This means you can track how BGP routing decisions affect traffic paths across AWS, Azure, GCP, and your data centers simultaneously. For organizations using cloud interconnects like Direct Connect, ExpressRoute, or Cloud Interconnect, Kentik correlates BGP route changes with interconnect performance so you can see when a routing event is degrading cloud connectivity — and act before users notice.