Oracle Cloud Infrastructure Observability
Know everything about your distributed cloud network.
Understand health of every workload
- Visualize traffic end-to-end across OCI, AWS, Google Cloud, and virtualized infrastructure for enterprise applications from AI to ZFS.
- Troubleshoot large-scale workloads used for disaster recovery, storage, back office operations, machine learning, model training, and more.
Migrate seamlessly
- Plan migrations to and from OCI with full visibility (translation: without costly rework).
- Move, duplicate, and optimize applications for peak reliability at lower cost.
- Baseline and alert on network behavior and application performance.
Optimize performance
- Understand and protect performance with autonomous testing and alerts.
- Discover OCI resources and monitor performance across clouds and service meshes.
- Investigate anomalies efficiently with ad-hoc tests for network connectivity, BGP routes, and application responses.
Cloud observability for telcos
- Achieve optimal network operations across private, hybrid, and public clouds.
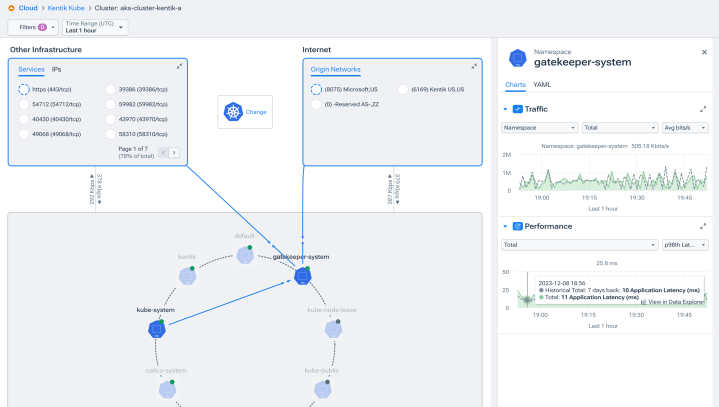
- Incorporate Kubernetes visibility seamlessly into monitoring.
- Ensure network modernization success in projects like cloud-based 5G and Open RAN.
Explore the platform
FAQs about Kentik for Oracle Cloud Infrastructure
What OCI data sources does Kentik ingest?
Kentik ingests three core telemetry types from Oracle Cloud Infrastructure: VCN flow logs (managed through OCI Logging in JSON format and delivered to an OCI Object Storage bucket), OCI metadata via API (tenancies, compartments, VCNs, subnets, VNICs, security lists, network security groups, route tables, FastConnect circuits, Dynamic Routing Gateways, and other infrastructure context), and metrics from OCI Monitoring for performance monitoring of OCI network services. Together, these provide complete visibility into traffic patterns, topology, and performance across OCI environments. For Oracle Kubernetes Engine (OKE), Kentik also supports the eBPF-based Kentik Kappa agent for pod-level Kubernetes traffic visibility.
How is Kentik deployed on OCI?
Kentik is delivered as SaaS, so there’s no on-premises infrastructure to deploy. OCI setup involves a five-step workflow in OCI plus one step in Kentik: configure an OCI Object Storage bucket to receive flow logs, enable VCN flow logs at the VCN, subnet, or VNIC level, configure an OCI Connector to forward the logs, create an OCI Policy granting the necessary permissions, and configure a “cloud export” in the Kentik portal with your tenancy ID, compartment ID, user ID, and region. The OCI configuration can also be automated through the Kentik Cloud Export API. Once configured, Kentik begins ingesting flow logs and metadata automatically.
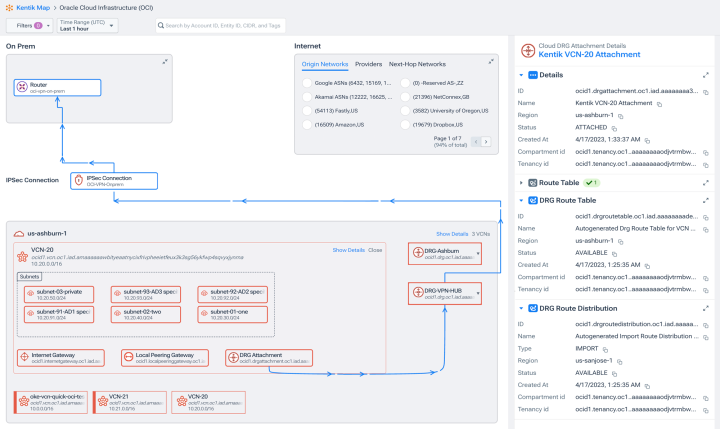
How does Kentik monitor traffic across OCI FastConnect and Site-to-Site VPN?
Kentik provides unified visibility across OCI’s hybrid connectivity services by combining VCN flow logs, OCI metadata, and OCI Monitoring metrics from FastConnect circuits, Site-to-Site VPN tunnels, and Dynamic Routing Gateways. For FastConnect, Kentik shows utilization, performance, and traffic distribution across each connection, making it possible to monitor connectivity between on-premises data centers and OCI regions. For Site-to-Site VPN tunnels and DRG-connected networks, traffic flows can be traced end-to-end alongside on-premises NetFlow data — giving teams the visibility to troubleshoot hybrid connectivity issues without switching between OCI-native and on-premises tools.
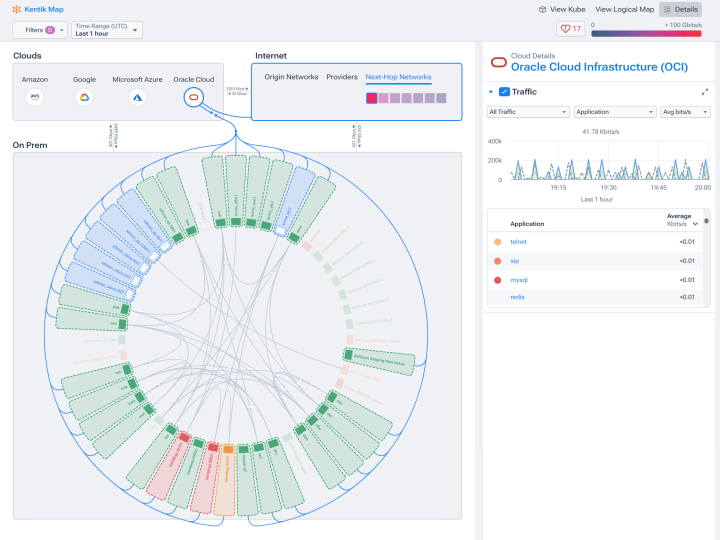
How do I monitor inter-region and inter-Availability Domain performance in OCI?
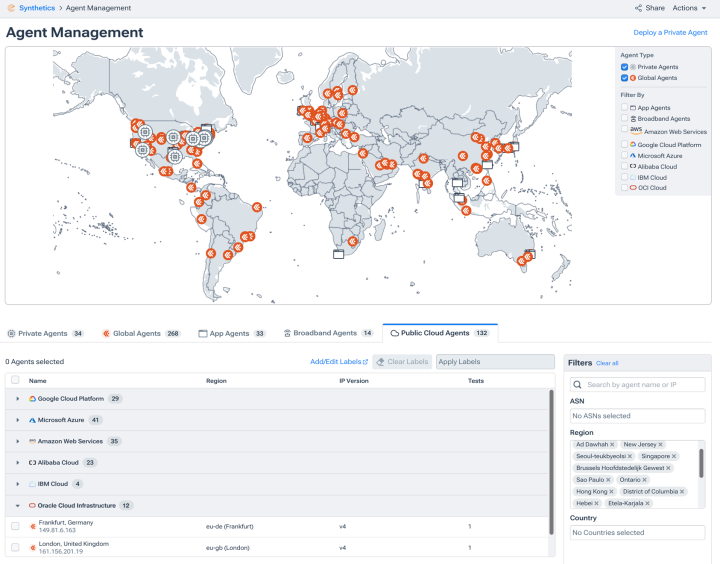
Inter-region and inter-Availability Domain monitoring requires correlating VCN flow logs with OCI metadata (which regions and ADs each resource belongs to) and synthetic tests between locations. Kentik supports this by automatically tagging flow records with region and AD information from OCI APIs, surfacing inter-region and inter-AD traffic patterns in the Kentik Map for OCI, and running synthetic tests from agents deployed in different OCI regions to measure latency, loss, and reachability between them. This makes it possible to detect performance regressions on specific paths, identify suboptimal routing decisions, and attribute the cost of cross-region or cross-AD data transfer to specific applications or business units.
How does Kentik help reduce OCI data transfer and egress costs?
OCI data transfer charges accumulate from inter-region traffic, FastConnect egress, internet egress, and traffic between OCI services — and most teams have limited visibility into which applications and workloads are driving the cost. Kentik analyzes VCN flow logs to surface the highest-cost flows, attribute traffic to specific compartments, VCNs, services, or business units, and identify suboptimal routing decisions (for example, traffic crossing regions unnecessarily, or traveling over the public internet when a private path through FastConnect is available). Teams use this data to optimize architecture, negotiate Oracle pricing with evidence, and reduce monthly data transfer spend.
How does Kentik handle Kubernetes networking in Oracle Kubernetes Engine (OKE)?
For OKE, Kentik provides pod-level network visibility through the Kentik Kappa agent, an eBPF-based agent that captures container traffic without sidecar deployment overhead. Kappa surfaces pod-to-pod and pod-to-service traffic, including key performance indicators like retransmit rate and out-of-order packet rate, and correlates that traffic with the underlying VCN and OCI infrastructure context. This makes it possible to investigate microservice performance issues at both the Kubernetes layer and the OCI network layer in a single platform — useful when OKE performance problems turn out to have causes in VCN routing, security list rules, or OCI network paths.
How does Kentik visualize traffic between OCI and other clouds?
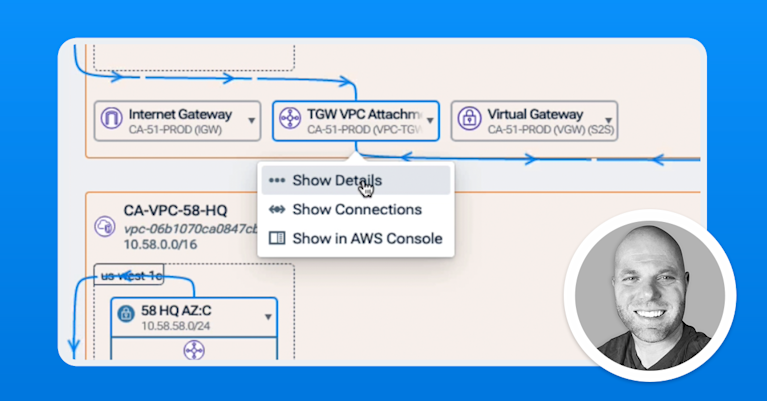
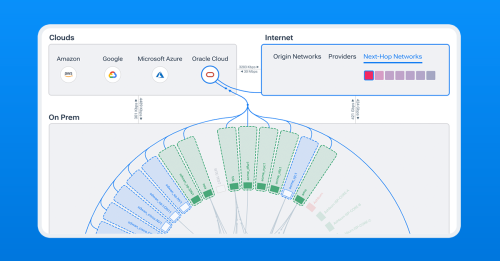
Kentik visualizes traffic end-to-end across OCI, AWS, Google Cloud, Azure, on-premises data centers, SD-WAN, and the public internet in a single platform. Flow logs from each cloud provider, plus on-premises NetFlow data, are normalized and enriched at ingest so that traffic between any combination of environments can be traced, attributed, and analyzed. The Kentik Map for OCI automatically renders hybrid and multi-cloud topology, making it possible to investigate cross-cloud performance issues — for example, when an application in OCI depends on a service in AWS, or when migration traffic moves between OCI and another provider — without switching between cloud-specific tools.
How does Kentik compare to OCI native monitoring tools?
OCI native monitoring (OCI Monitoring, OCI Logging, OCI Network Visualizer, Operations Insights) is essential for OCI-specific operational visibility, but it’s scoped to OCI itself. Kentik complements OCI native tooling by providing cross-environment analytics — correlating OCI traffic with on-premises NetFlow, multi-cloud telemetry from AWS, Azure, and GCP, BGP routing, and internet path data — and by adding capabilities OCI native tools don’t provide, including ingest-time enrichment with BGP and AS path metadata, flow-level forensics across hybrid environments, cloud egress cost analytics with attribution by compartment and business unit, synthetic testing from globally distributed agents, and AI-driven investigation through Kentik AI Advisor. Most teams use both: OCI native tools for OCI-specific operations and Kentik for the cross-environment network intelligence that OCI native tools weren’t designed to deliver.